Over the last ten to fifteen years, the way we interact with technology at work has fundamentally shifted. Once, it was common to travel to
Category: Data Protection
Apr 24, 2025Ravie LakshmananPhishing / Cybercrime The threat actors behind the Darcula phishing-as-a-service (PhaaS) platform have released new updates to their cybercrime suite with generative

“I built an automation that cloned and scanned tens of thousands of public GitHub repos for leaked secrets,” Brizinov said in a blog post. “For
A significant security gap in Linux runtime security caused by the ‘io_uring’ interface allows rootkits to operate undetected on systems while bypassing advanced Enterprise security

Supply chain attacks are becoming an increasingly common strategy for hackers. They’ll generally target organizations via third-party suppliers, partners, or vendors, all of whom might
The majority of ransomware attacks target small businesses, according to Verizon’s latest Data Breach Investigations Report (DBIR), with extortion malware appearing in 88% of SMB
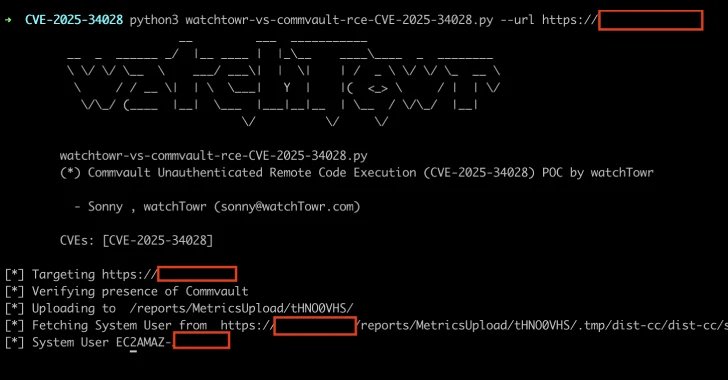
Apr 24, 2025Ravie LakshmananData Breach / Vulnerability A critical security flaw has been disclosed in the Commvault Command Center that could allow arbitrary code execution

Google has warned remote workers will need to return to the office or else lose their jobs, according to reports. Internal documents viewed by CNBC
The Evolving Healthcare Cybersecurity Landscape Healthcare organizations face unprecedented cybersecurity challenges in 2025. With operational technology (OT) environments increasingly targeted and the convergence of IT

IBM has revealed 15 contracts agreed with the US government have been shelved amid a cost-cutting drive implemented by the Trump administration. The tech giant