A misconfigured tracking tool on Blue Shield of California’s websites exposed the protected health information (PHI) of 4.7 million members to Google Ads over a
Category: Data Protection

Microsoft announced an increase in bug bounty payouts to $30,000 for AI vulnerabilities found in Dynamics 365 and Power Platform services and products. Power Platform
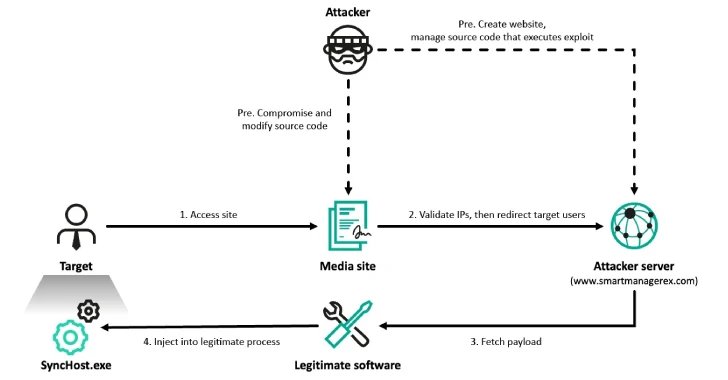
Apr 24, 2025Ravie LakshmananMalware / Threat Intelligence At least six organizations in South Korea have been targeted by the prolific North Korea-linked Lazarus Group as

Yale New Haven Health (YNHHS) is warning that threat actors stole the personal data of 5.5 million patients in a cyberattack earlier this month. YNHHS

Ransomware attacks continue to climb, but they may be even higher than official figures show as companies choose to quietly pay to make such incidents

A new critical vulnerability has been found in Commvault, illustrating that backup and replication solutions are highly sought after by cyber threat actors due to

Microsoft says it resolved a known issue causing erroneous 0x80070643 installation failure errors when deploying the April 2025 Windows Recovery Environment (WinRE) updates. When it
Apr 24, 2025Ravie LakshmananEndpoint Security / Linux Cybersecurity researchers have demonstrated a proof-of-concept (PoC) rootkit dubbed Curing that leverages a Linux asynchronous I/O mechanism called

Apr 24, 2025Ravie LakshmananVulnerability / Threat Intelligence As many as 159 CVE identifiers have been flagged as exploited in the wild in the first quarter

Der weltweite Durchschnitt für Lösegeldzahlungen liegt bei 479.000 Dollar, in Indien bei 4,8 Millionen Dollar. Dies zeigt, dass die Angreifer ihre Forderungen je nach Region
