The Acer Aspire 14 AI might be the epitome of the mid-sized, mid-range laptop. It’s compact and relatively light, with a 14-inch screen but still
Category: Data Protection

The cybersecurity community has reacted with shock and bewilderment at a decision by the US government not to renew MITRE’s contract to manage the Common

What does PAM stand for – Privileged Account Management or Privileged Access Management? Well, this is the acronym used for both terms, but keep in mind these are not exactly synonyms.
Cheap Android smartphones manufactured by Chinese companies have been observed pre-installed with trojanized apps masquerading as WhatsApp and Telegram that contain cryptocurrency clipper functionality as

High energy consumption, raw material requirements, and physical space constraints are holding back data center sustainability efforts, according to new research from Seagate. With Goldman
Whether we’re referring to IAM or PAM, there are several factors that make these policies a unique challenge. Much of this comes down to the
Apr 16, 2025Ravie LakshmananVulnerability Management / Incident Response The U.S. government funding for non-profit research giant MITRE to operate and maintain its Common Vulnerabilities and

MITRE Vice President Yosry Barsoum has warned that U.S. government funding for the Common Vulnerabilities and Exposures (CVE) and Common Weakness Enumeration (CWE) programs expires
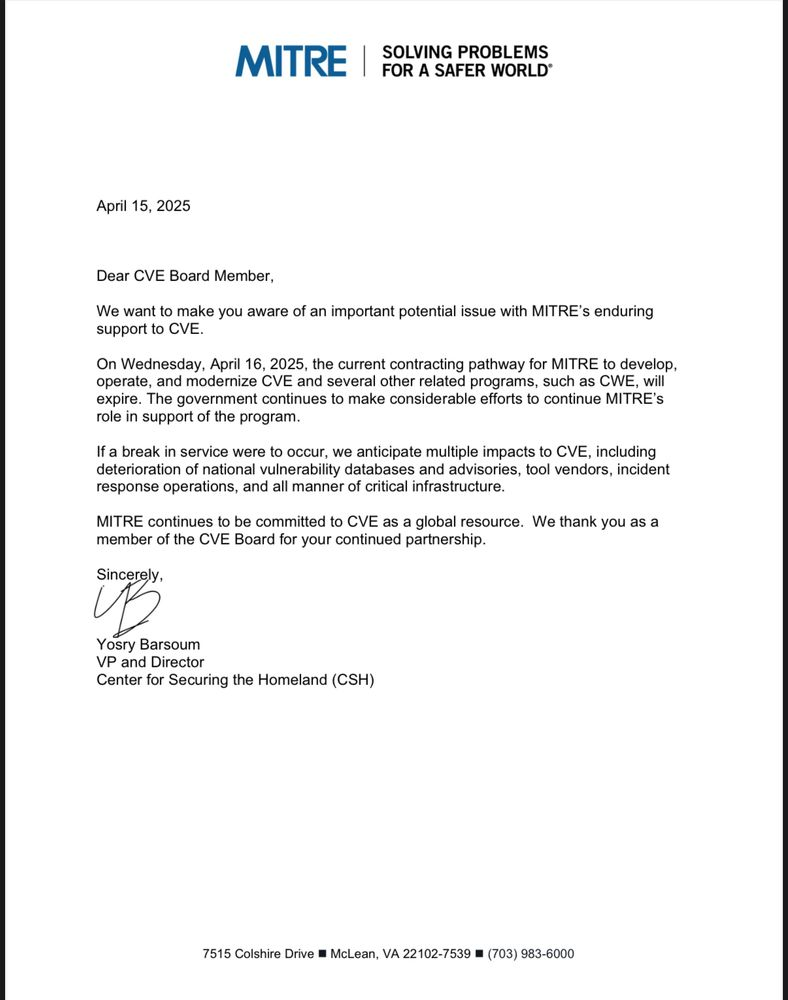
A critical resource that cybersecurity professionals worldwide rely on to identify, mitigate and fix security vulnerabilities in software and hardware is in danger of breaking

Sie kennen Stücklisten vielleicht im Zusammenhang mit Neuwagen. In diesem Fall handelt es sich um ein Dokument, das jede Komponente, die sich in Ihrem neuen
