Some of the world’s most popular large language models (LLMs) are producing insecure code by default, according to a new analysis by Backslash Security. The
Category: Data Protection
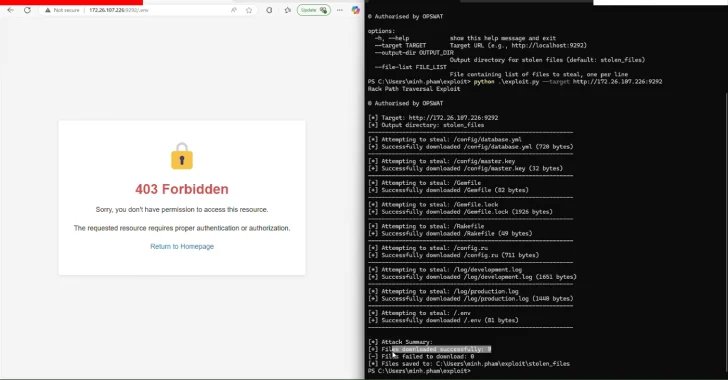
Apr 25, 2025Ravie LakshmananVulnerability / Data Breach Cybersecurity researchers have disclosed three security flaws in the Rack Ruby web server interface that, if successfully exploited,

“Because they operate at this critical boundary, they often hold elevated privileges and have broad visibility into internal systems,” Linares noted, adding that edge devices

The vast majority of phishing attacks against the healthcare sector go unreported to security teams, leaving organizations unable to fully learn from their mistakes. In
Das Portal von guenstiger.de ist online – was die Hacker jedoch im Backend angerichtet haben, darüber liegen noch keine Informationen vor. guenstiger.de Das deutsche Preisvergleichsportal

JennaWagner/Getty Images Out of the blue, I received a text from my father asking me, “What’s the difference between a password and a passkey?” Somewhere,

Microsoft says it will soon fix a known issue causing CPU spikes when typing messages in recent versions of its classic Outlook email client. Redmond
Intel’s new CEO Lip-Bu Tan has confirmed the company will be cutting its headcount in response to sluggish revenue. In an investor call, reported by

Fazit Diese allgemeinen Ergebnisse zeigen bereits die größten Problemfelder auf. Dennoch ist es wichtig, im Rahmen eines Datenrisiko-Assessments das individuelle Datenrisiko zu ermitteln und Schwachpunkte
The bigger question for a CISO to consider, he added, is whether data sharing with a third party is part of their threat model. There
