Mar 24, 2025Ravie LakshmananVulnerability / Web Security A critical security flaw has been disclosed in the Next.js React framework that could be potentially exploited to
Category: Data Protection

Creating a national continuity policy Under the EO, within 180 days (by Sept. 15) the APNSA, in coordination with the heads of relevant agencies, must

Xuanyu Han/Getty Images A phishing attack that previously hit Windows users has now switched its target to the Mac. In a report published Wednesday, security

Dave Cottlehuber, the founder of SkunkWerks, a small tech infrastructure firm in Austria, says he has been moving the company’s few servers and databases away
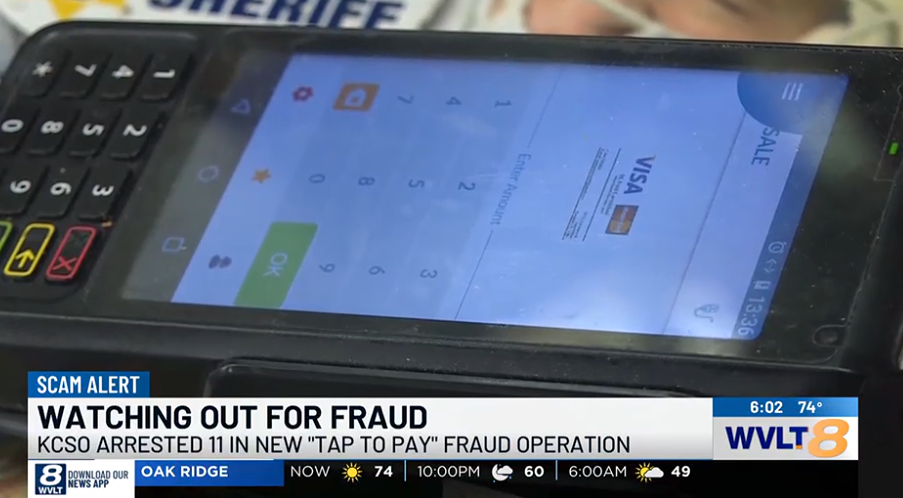
Authorities in at least two U.S. states last week independently announced arrests of Chinese nationals accused of perpetrating a novel form of tap-to-pay fraud using

Cybercriminals are abusing Microsoft’s Trusted Signing platform to code-sign malware executables with short-lived three-day certificates. Threat actors have long sought after code-signing certificates as they can

Table of Contents Close Table of Contents Key Takeaways: Where to Watch Beyond Paradise Sign up for NordVPN at a 72% discount. There’s a 30-day
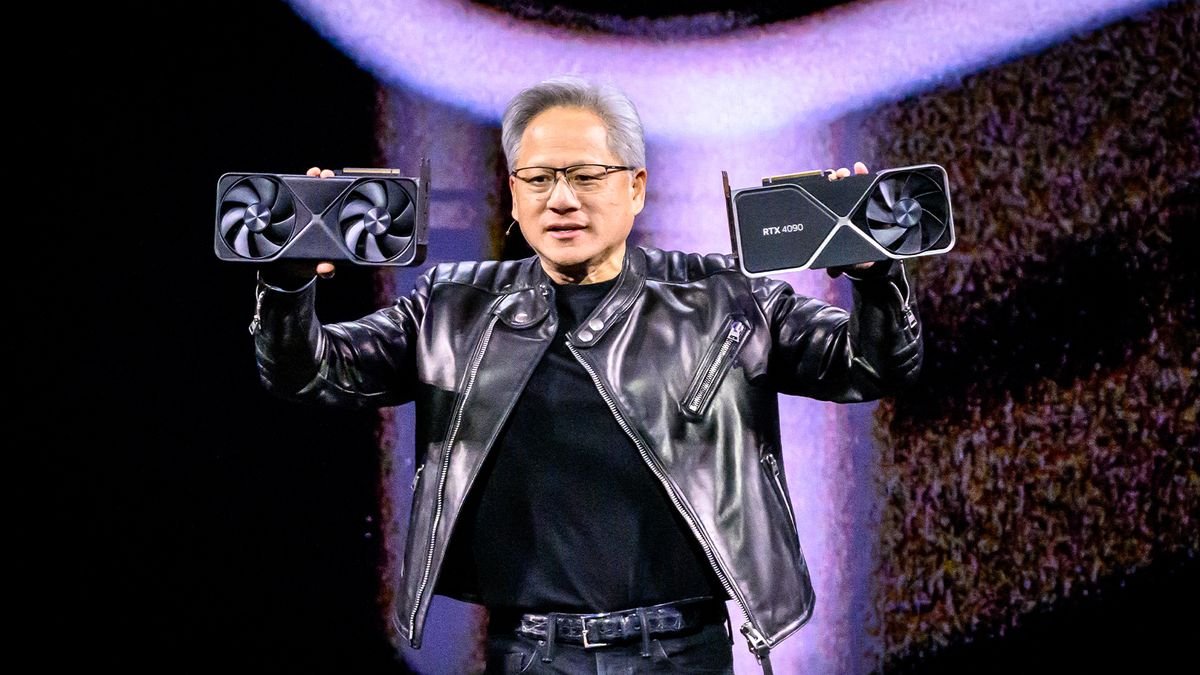
Nvidia GTC 2025, the chipmaker’s annual conference, has dominated the airwaves this week – and it’s not hard to see why. The company is the

In today’s world, cybersecurity is more critical than ever. Organizations and individuals alike face a constant barrage of cyber threats, and often, the weakest link

Online scams are evolving faster than ever, with cybercriminals using AI, deepfake technology, and social engineering to trick unsuspecting users. In the past year, Americans
