“A boxer derives the greatest advantage from his sparring partner…”— Epictetus, 50–135 AD Hands up. Chin tucked. Knees bent. The bell rings, and both boxers
Category: Data Protection

Open source systems are now deeply embedded across technology stacks, from Android devices to mission-critical enterprise systems and, of course, AI. There are businesses built

Inauguration Day has come and gone, and the peaceful transfer of power couldn’t have happened without the intricate systems that ensure the integrity of the

Mar 26, 2025Ravie LakshmananSupply Chain Attack / Malware Cybersecurity researchers have discovered two malicious packages on the npm registry that are designed to infect another

The Kubernetes project has released patches for five vulnerabilities in a widely used popular component called the Ingress NGINX Controller that’s used to route external

Matt Clifford is a name that keeps popping up in UK tech: a successful investor, Clifford also leads innovation and science as chair of the
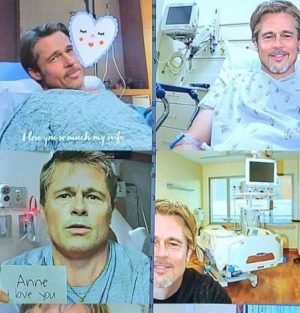
Romance scams have surged in sophistication, preying on emotions and exploiting the trust of victims in the digital age. The latest case involving a French

Mar 26, 2025The Hacker NewsRansomware / Endpoint Security The Russian-speaking hacking group called RedCurl has been linked to a ransomware campaign for the first time,

Sie können nicht sagen, wir hätten Sie nicht gewarnt… Foto: Anton Vierietin | shutterstock.com CISOs und andere Executives im Bereich IT-Sicherheit arbeiten im Regelfall hart
OpenAI has announced a slew of new cybersecurity initiatives, including a 500% increase to the maximum award for its bug bounty program. In a blog
