Not only does the incident response plan lead to better cost estimates, but it will also lead to a quicker return of network functions. “Practice,
Author:

Not only does the incident response plan lead to better cost estimates, but it will also lead to a quicker return of network functions. “Practice,

Over the past decade, encrypted communication has become the norm for billions of people. Every day, Signal, iMessage, and WhatsApp keep billions of messages, photos,
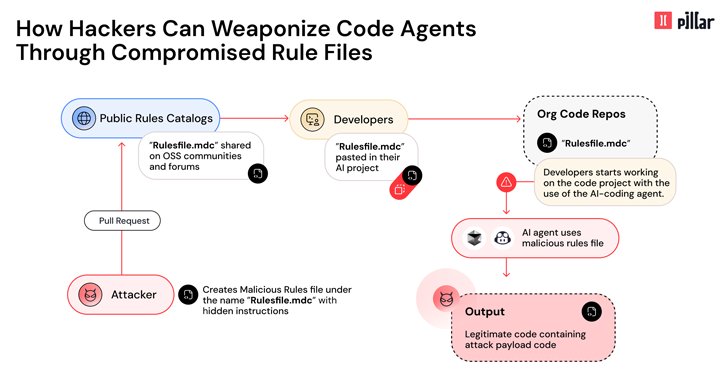
Mar 18, 2025Ravie LakshmananAI Security / Software Security Cybersecurity researchers have disclosed details of a new supply chain attack vector dubbed Rules File Backdoor that

If you’re looking for PDQ Deploy alternatives, you’re either aware of the product’s limitations or exploring your options. As one user puts it: While PDQ

If you’re looking for PDQ Deploy alternatives, you’re either aware of the product’s limitations or exploring your options. As one user puts it: While PDQ

If you’re looking for PDQ Deploy alternatives, you’re either aware of the product’s limitations or exploring your options. As one user puts it: While PDQ

If you’re looking for PDQ Deploy alternatives, you’re either aware of the product’s limitations or exploring your options. As one user puts it: While PDQ

Cybercriminals used information-stealing malware to a devastating effect last year, capturing sensitive data that fueled ransomware, breaches and attacks targeting supply chains and critical infrastructure,

Mar 19, 2025Ravie LakshmananVulnerability / DevSecOps The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a vulnerability linked to the supply chain compromise